Today, cybersecurity has become a priority for all organizations, large or small. With the increasing reliance on technology and data, cyber threats have become more sophisticated and dangerous. Therefore, it is critical for companies to constantly assess and strengthen their cybersecurity protection levels. But what levels of protection exist and what does each include? In this article, we will explore these levels to help you better understand how to protect your organization.
Basic Level of Protection
The basic level of protection is the starting point for any organization looking to secure its systems and data. This level includes the essential security measures that all companies should implement, regardless of their size or industry.
1. Firewalls: Firewalls act as a barrier between your internal network and external threats, filtering traffic and blocking unauthorized access.
2. Antivirus: Antivirus programs are essential to detect, prevent and eliminate malicious software, known as malware, that can damage your systems or steal sensitive information.
3. Backups: Backing up your data regularly allows you to recover important information in the event of a cyber attack, such as ransomware that encrypts your files and demands a ransom to free them.

Intermediate Level of Protection
Once your organization has implemented the basic level of protection, it is time to advance to the intermediate level. This level includes additional measures to strengthen your security and better protect your information against more advanced threats.
1. Access controls: Implementing robust access controls ensures that only authorized personnel can access critical information. This is achieved through authentication systems, such as strong passwords, two-factor authentication or biometric recognition.
2. Data encryption: Encryption turns your data into a code unreadable to anyone who does not have the encryption key. This is an additional layer of protection for your data, both at rest and in transit.
3. Network security: Enhancing the security of your network can include network segmentation, which separates critical resources from less sensitive parts of the network, thus reducing the risk of unauthorized access to key areas.
Advanced Level of Protection with ISO 27001
The advanced level of protection is the most comprehensive and is recommended for organizations that handle large volumes of sensitive data or are in highly regulated industries. This level includes proactive and reactive strategies to address the most sophisticated cyber threats, in addition to complying with international standards such as ISO 27001.
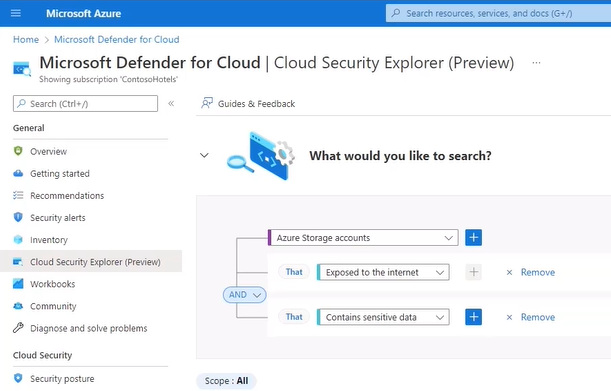
Microsoft Defender for Cloud is one of the tools we use to perform a complete risk analysis.
1. ISO 27001: Adopting ISO 27001 implies a commitment to information security at the organizational level. This standard requires companies to systematically assess information security risks and design controls to mitigate or eliminate those risks. Implementing ISO 27001 not only improves security but also provides a strong signal to customers and partners that the company takes data protection seriously.
2. Risk analysis: By aligning with ISO 27001, risk analysis becomes an ongoing activity that assists in the proactive identification of vulnerabilities and threats, enabling appropriate and documented control measures to be implemented as part of the ISMS.
3. Incident management and emergency response plans: These systems are strengthened by ISO 27001, establishing detailed and tested procedures for handling information security incidents. This includes not only immediate response but also post-incident recovery and prevention of future events.
Cybersecurity is a critical element for the operation and reliability of any organization in the digital era. By progressing through the levels of protection and eventually implementing and certifying to ISO 27001, companies not only protect their information assets but also demonstrate a commitment to information security excellence. Adopting ISO 27001 can differentiate an organization in the marketplace, improve customer confidence and ensure long-term resilience against cyber threats. Keeping up to date with the latest trends and technologies in cybersecurity is essential, and investing in these levels of protection translates into protecting not only data and systems but also reputation and business continuity.
If you want your company to have an advanced level of protection, you can contact us to analyze the structure of your organization. We offer you a specialized cybersecurity team that provides 24/7 protection by performing an analysis of all your networks, databases or applications to detect any anomaly that may compromise the security of the company to take appropriate containment measures. If you want to know more about the activities performed by our team you can visit this link.